Mobile Phishing Attack Vectors 2026: Why Your Phone Is the Easiest Door into Your Organization
Nearly half of all data breaches now start on mobile devices. Discover the attack vectors transforming phones into enterprise security's greatest vulnerability—and how to defend across SMS, voice, QR codes, and messaging apps.
The Mobile Threat Reality
Nearly one in two data breaches now originates on a mobile device. Your phone is no longer just a convenience — for attackers, it's the easiest door into your organization.
The laptop is no longer the primary target. The battlefield has shifted to the device you carry everywhere, check 150 times a day, and trust implicitly because it feels personal. According to the Verizon 2025 Data Breach Investigations Report, mobile-initiated phishing and social engineering now account for 47% of all confirmed data breaches globally, a figure that has more than doubled since 2021.
This isn't a coincidence. It's a calculated pivot by cybercriminals who have mapped your behavior, your habits, and the exact reasons why you're more likely to click a malicious link on a phone than on a desktop.
Let's break down exactly how mobile phishing attacks work, what makes phones uniquely exploitable, and how modern organizations and individuals can fight back.
Why Phones Are the New Phishing Goldmine
The Psychological Advantage of Mobile
Mobile devices create a perfect storm of psychological vulnerabilities that attackers exploit deliberately:
- Condensed UI: Mobile browsers hide full URLs, so
secure-bankofamerica.verify-login.xyzlooks like a trusted site - Constant connectivity: Notifications arrive in real time, creating urgency before you can think critically
- Context switching: You check messages while distracted — in meetings, commuting, half-awake at 7am
- Personal trust: Your phone feels intimate. A WhatsApp message feels more trustworthy than a cold email
Mobile phishing works because the device is designed to minimize friction. Unfortunately, friction is often what gives us time to think.
Mobile Attack Surfaces Are Multiply Larger
| Channel | Desktop Risk | Mobile Risk | Why Higher on Mobile |
|---|---|---|---|
| High | High | No hover-to-preview URLs | |
| SMS/iMessage | Low | Critical | Native trust, no spam filters |
| WhatsApp/Telegram | Medium | Very High | Encrypted, evades scanners |
| QR Codes | Low | High | No URL visible before scanning |
| App Stores | N/A | Medium | Rogue apps mimic legitimate ones |
| Push Notifications | N/A | High | Opens apps directly |
The Major Mobile Phishing Attack Vectors in 2026
1. Smishing — SMS Phishing

Smishing (SMS + phishing) is the most widespread mobile attack vector. The APWG Phishing Trends Report Q4 2025 recorded a 328% year-on-year increase in smishing campaigns.
The anatomy of a smishing attack:
- You receive an SMS that appears to come from your bank, delivery service, or government agency
- The message creates urgency: "Your parcel is stuck. Pay ₹35 customs fee within 24 hours"
- The link leads to a pixel-perfect clone of a legitimate site
- You enter credentials or payment details — and they're harvested instantly
SMS messages have a 98% open rate compared to 20% for email. Attackers know this. They also know most corporate MDM (Mobile Device Management) solutions don't scan SMS content in real time, making it a nearly blind channel for enterprise security teams.
2. Vishing — Voice Call Phishing
Vishing uses phone calls, now supercharged with AI voice cloning, to impersonate:
- Your bank's fraud department
- The IRS, income tax department, or UIDAI
- Your company's IT helpdesk
- A family member in an emergency ("grandparent scams")
In 2025, attackers began using real-time voice deepfakes that can clone a known person's voice from as little as 3 seconds of audio scraped from social media. The FBI's Internet Crime Complaint Center (IC3) reported losses exceeding $1.1 billion from vishing and deepfake voice attacks in 2025.
The attack flow:
- Attacker scrapes executive's voice from LinkedIn video or earnings call
- Deepfake voice engine generates real-time audio mimicking the executive
- Employee receives call from "CFO" authorizing an urgent wire transfer
- Transfer is approved. Funds reach the attacker's mule account within minutes
3. Quishing — QR Code Phishing
Quishing (QR + phishing) has surged as QR codes became mainstream during and after COVID-19. Attackers:
- Replace restaurant menus or parking payment QR codes with malicious ones
- Embed malicious QR codes in phishing emails (bypassing email URL scanners entirely)
- Print fake QR codes on stickers and overlay them on legitimate flyers
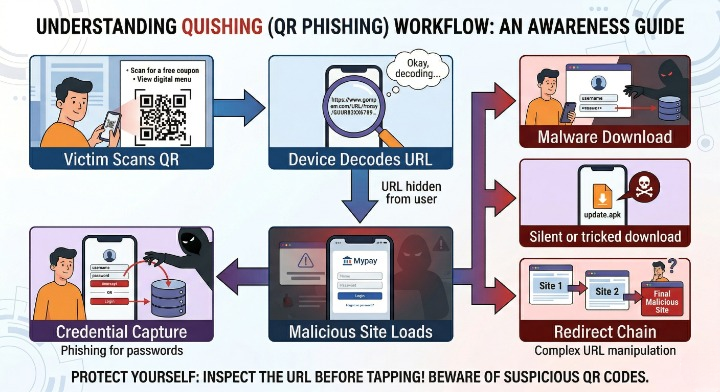
Since QR codes encode URLs in an image format, traditional email and web filters cannot scan them — making quishing one of the fastest-growing mobile attack methods of 2025–2026.
4. Malicious Mobile Apps
Threat actors publish lookalike apps on official stores using:
- Names one character off from legitimate apps (
PayPaIvsPayPal) - Fake reviews and inflated download counts
- Legitimate-looking screenshots copied from the real app
Once installed, these apps may:
- Overlay a fake UI on top of your banking app to steal credentials (overlay attacks)
- Act as stalkerware, silently forwarding SMS OTPs to the attacker
- Record keystrokes or take periodic screenshots
Indian CERT-In reported over 120 lookalike UPI apps flagged in 2025, targeting users of PhonePe, Google Pay, and BHIM. Many remained on third-party Android stores for weeks before takedown.
5. Social Media and Messaging App Phishing
According to the Zscaler ThreatLabz 2025 Phishing Report, Telegram has become one of the top platforms cybercriminals exploit — used not just for impersonating trusted brands, but also for distributing malware and coordinating attacks. On mobile, these threats are amplified because:
- Users are already authenticated and in a socially trusting environment
- Fraudulent profiles can convincingly impersonate mutual contacts or colleagues
- In-app link previews make malicious URLs appear legitimate before anyone even taps them
Who Is Being Targeted? The Mobile Phishing Victim Profile
Mobile phishing attacks are no longer random spam blasts. They are precision-targeted operations using data from breaches, social media, and corporate directories.
High-Risk Groups in 2026
| Target Group | Attack Vector | Typical Lure |
|---|---|---|
| C-suite executives | Vishing + email | Board meeting urgency, wire fraud |
| HR & Finance teams | Smishing + email | Payroll changes, fake invoices |
| Remote workers | Fake VPN/MDM apps | "Update required to maintain access" |
| Students & educators | Smishing | Fee outstanding, scholarship alerts |
| Healthcare staff | Hybrid (call + SMS) | Patient record access, schedule changes |
| General public (India) | Smishing (UPI, Aadhaar) | KYC suspension, tax refund pending |
No group is immune, but the attack vectors are becoming highly tailored to each target's daily workflow.
Executive and IT teams are being hit by a resurgence of voice-based attacks. Voice phishing climbed to the second-most common initial infection vector in 2025, appearing in 11% of Mandiant's investigations where a vector could be identified — while email phishing, which was the dominant social engineering vector just a few years ago, has seen a sustained decline. The reason is structural: interactive social engineering methods require live human engagement and are significantly more resistant to automated technical controls than volume-based email campaigns.
For cloud environments specifically, the picture is even more stark. Voice phishing accounted for 23% of cloud-related intrusions in 2025, followed by third-party compromise at 17%, stolen credentials at 16%, email phishing at 15%, and insider threats at 14%.
Indian users face a uniquely localized threat layer. Data from the Ministry of Home Affairs and the Indian Cyber Crime Coordination Centre shows that UPI-based fraud continued to lead in volume and value through 2025, with most incidents involving phishing links, counterfeit QR codes, remote-access apps, or SIM-swap operations. The scale is significant: a LocalCircles survey of over 32,000 respondents across 365 districts found that 1 in 5 families using UPI experienced fraud since 2022 — with 40% of victims losing money after clicking fraudulent payment links shared via SMS, WhatsApp, or social media. Making matters worse, 51% of those who experienced UPI fraud did not file any official complaint, suggesting the true scale of the problem is far higher than official figures reflect.
The lures are effective because they exploit real anxiety around government infrastructure. Fraudsters impersonate RBI representatives, UPI support desks, and even bank grievance cells to manufacture urgency. And the technology behind these attacks is evolving rapidly: voice cloning has become so sophisticated that a few seconds of audio from social media is enough to mimic a family member or an official.
Industries Most Targeted by Mobile Phishing (2025 Attack Data)
| Rank | Industry | Share of Attacks |
|---|---|---|
| 1 | Technology | 17.0% |
| 2 | Financial Services | 14.6% |
| 3 | Business & Professional Services | 13.3% |
| 4 | Healthcare | 11.9% |
| 5 | Others | 43.2% |
Source: Mandiant M-Trends 2026 Report
The high-tech sector led all industries in share of Mandiant investigations in 2025, surpassing financial services, which had led for the two prior years. The shift reflects attackers following where the access is most valuable — technology companies hold credentials, tokens, and SaaS integrations that unlock downstream targets far beyond the initial victim.
The M-Trends 2026 report is grounded in over 500,000 hours of frontline incident investigations conducted by Mandiant globally in 2025, making it one of the most comprehensive datasets on real-world attacker behaviour available today.
The Anatomy of a Modern Mobile Phishing Campaign
Understanding how these attacks are built helps organizations defend against them more effectively.
Infrastructure Behind a Mobile Phishing Attack
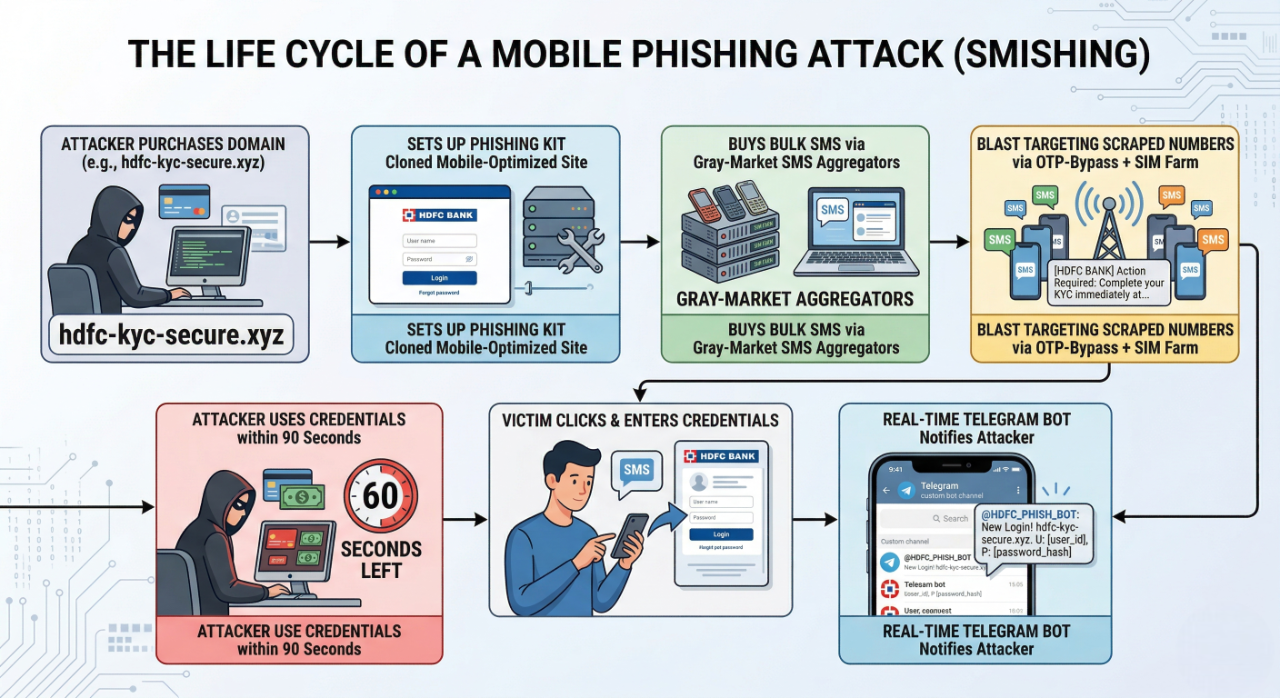
The most chilling detail: the median time between a victim submitting credentials and an attacker using them is under 2 minutes, according to Google's Safe Browsing Transparency Report 2025.
Why Mobile Phishing Sites Are Harder to Detect
- HTTPS Everywhere: Attackers use free TLS certificates, making malicious sites appear "secure"
- Short-lived domains: Many phishing domains are registered and abandoned within 72 hours, before threat intelligence lists can flag them
- Mobile-specific cloaking: Sites serve benign content to security scanners (desktop IPs, known bot user-agents) but malicious content to mobile browsers
Defending Against Mobile Phishing Attacks
For Individuals: The Mobile Security Checklist
- Never click links directly from SMS/WhatsApp — type URLs manually or use bookmarks
- Enable caller ID and spam protection on your carrier and phone OS
- Install apps only from official stores and verify developer names carefully
- Use hardware security keys or authenticator apps instead of SMS OTPs for MFA
- Enable Google Play Protect or iOS App Attest for runtime app verification
- Report suspicious SMS to your carrier's spam short code (1909 in India, 7726 in the US/UK)
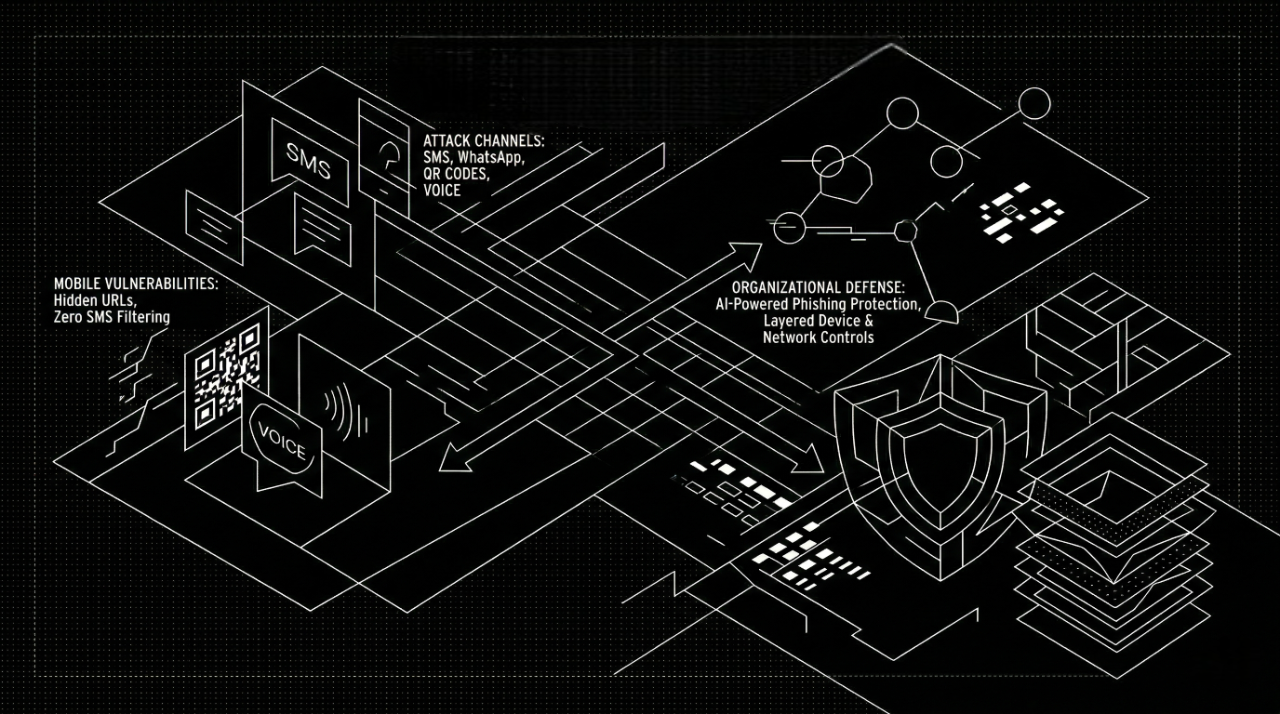
For Enterprises: A Layered Mobile Defense Architecture
Protecting an organization's mobile attack surface requires defense-in-depth across three layers:
Layer 1 — Device Layer (MDM/UEM)
- Enforce Mobile Device Management policies with remote wipe capability
- Block sideloading of unsigned APKs on Android devices
- Require OS version enforcement — most mobile exploits target unpatched devices
Layer 2 — Network Layer (Zero Trust Mobile Access)
- Route mobile traffic through DNS filtering to block known phishing domains
- Require device health attestation before granting access to corporate apps
- Deploy Mobile Threat Defense (MTD) agents that inspect app behavior at runtime
Layer 3 — Human Layer (Awareness + Simulation)
- Run mobile-specific phishing simulations — not just email. Include SMS, WhatsApp, and QR code scenarios
- Train employees to recognize deepfake voice cues (unnatural pacing, audio artifacts, unusual requests)
- Establish a one-call verification protocol for any financial request received on mobile
Organizations that implement mobile phishing simulation training reduce click-through rates on smishing campaigns by up to 76% in the first 90 days, according to Proofpoint's 2025 State of the Phish Report.
Real-World Mobile Phishing Breaches: Lessons Learned
Twilio: SMS Phishing at Scale
Twilio confirmed that attackers gained unauthorized access to internal systems after a sophisticated social engineering campaign stole employee credentials via SMS. The messages impersonated Twilio's IT department, urging employees to click URLs containing words like "Twilio," "Okta," and "SSO" that redirected to a cloned login page. The downstream damage was severe — attackers accessed 209 customer accounts and 93 Authy 2FA users, and registered their own devices to obtain temporary tokens. The contrast with Cloudflare — targeted in the same campaign but unbreached — is instructive: Cloudflare employees used FIDO2-compliant hardware security keys, which blocked login attempts even after credentials were stolen.
Uber: MFA Fatigue via WhatsApp
Uber confirmed that attackers used stolen credentials of an external contractor in an MFA fatigue attack — flooding the target with two-factor authentication requests until one was accepted. The attacker contacted the contractor on WhatsApp, posing as tech support, and told them to approve the MFA notification to make the flood of prompts stop. Once inside, the attacker found PowerShell scripts with privileged admin credentials, granting access to AWS, Google Cloud Platform, OneLogin, SentinelOne, and Slack. The lesson: MFA alone does not protect against prompt bombing — organizations should move to phishing-resistant methods such as number matching or hardware security keys.
Activision: One Text, One HR Employee
Activision confirmed a breach in December 2022 after hackers gained access to internal systems by tricking an HR employee with a single SMS phishing text. HR was the ideal target — their role requires fast responses to employee communications, making urgent-sounding texts harder to question. The compromised data included nearly 19,500 records — full names, phone numbers, job titles, locations, and email addresses of Activision staff. Making matters worse, employees only learned of the breach months later via Twitter screenshots — Activision had not disclosed it internally.
How AI Is Both the Threat and the Solution
AI Empowering Attackers
- Generative AI creates flawless phishing content in any language, at any scale
- Voice cloning models (ElevenLabs, Fish Speech) can clone a voice from 10 seconds of audio
- LLM-powered bots maintain convincing conversations with victims for hours on social media
- AI-generated deepfake faces are used in video call vishing attacks (Zoom/Teams)
AI Defending Against Mobile Phishing
Reactive, rule-based filters cannot keep up with AI-generated threats that are unique every time. Modern defense requires AI that works the same way attackers do — by understanding intent, not just matching patterns.
How Metis by AstraQ Protects Across Mobile Channels
While individuals can follow best practices, enterprises face a fundamentally different challenge: they cannot rely on human vigilance alone when thousands of employees carry smartphones that connect to corporate systems 24/7.
This is exactly the problem Metis, an AI-powered phishing detection platform, was built to solve.
Metis is a cross-platform phishing detection engine. It analyzes URLs, content, visual brand impersonation, and user behavior patterns to identify zero-day and AI-generated phishing attacks across email, web, and mobile channels — in real time.
What Makes Metis Different for Mobile Threat Protection
| Challenge | How Metis Addresses It |
|---|---|
| Short-lived phishing domains | Zero-day URL analysis with no dependency on threat intel lists |
| QR code phishing (quishing) | Image-based QR decoding and destination URL analysis |
| Mobile-optimized clone sites | Visual brand impersonation detection using computer vision |
| Smishing via SMS | Cross-channel integration with SMS gateway monitoring |
| Deepfake and AI-generated content | Behavioral anomaly scoring beyond content pattern matching |
| High false-positive fatigue | Adaptive risk scoring that trains on your organization's context |
Metis operates silently in the background — analyzing, scoring, and blocking threats before they reach your employees' thumbs. With zero-day attack identification, it catches the phishing campaigns that no blacklist has ever seen before.
Your Phone Is a Security Perimeter
The era of defending a corporate network perimeter is over. The perimeter is now wherever your employees' phones are — on a train, in a cafe, in bed at midnight when that urgent "IT helpdesk" SMS arrives.
Mobile phishing attacks have matured from clumsy spam campaigns into precision-engineered, AI-augmented operations that exploit the exact psychological vulnerabilities that make smartphones so useful. Nearly half of all breaches now start on a phone. That number will only grow.
The response cannot be awareness alone — it must be systematic, automated, and intelligent. Organizations that treat mobile security as an afterthought are not asking if they will be breached. They're asking when.
At AstraQ, we're building the tools that give defenders the same AI advantage that attackers already have. Explore Metis and make sure your organization's mobile channels are no longer the easiest door in.